Raging network devices vulnerabilities
- Sep 19, 2023
- 1 min read
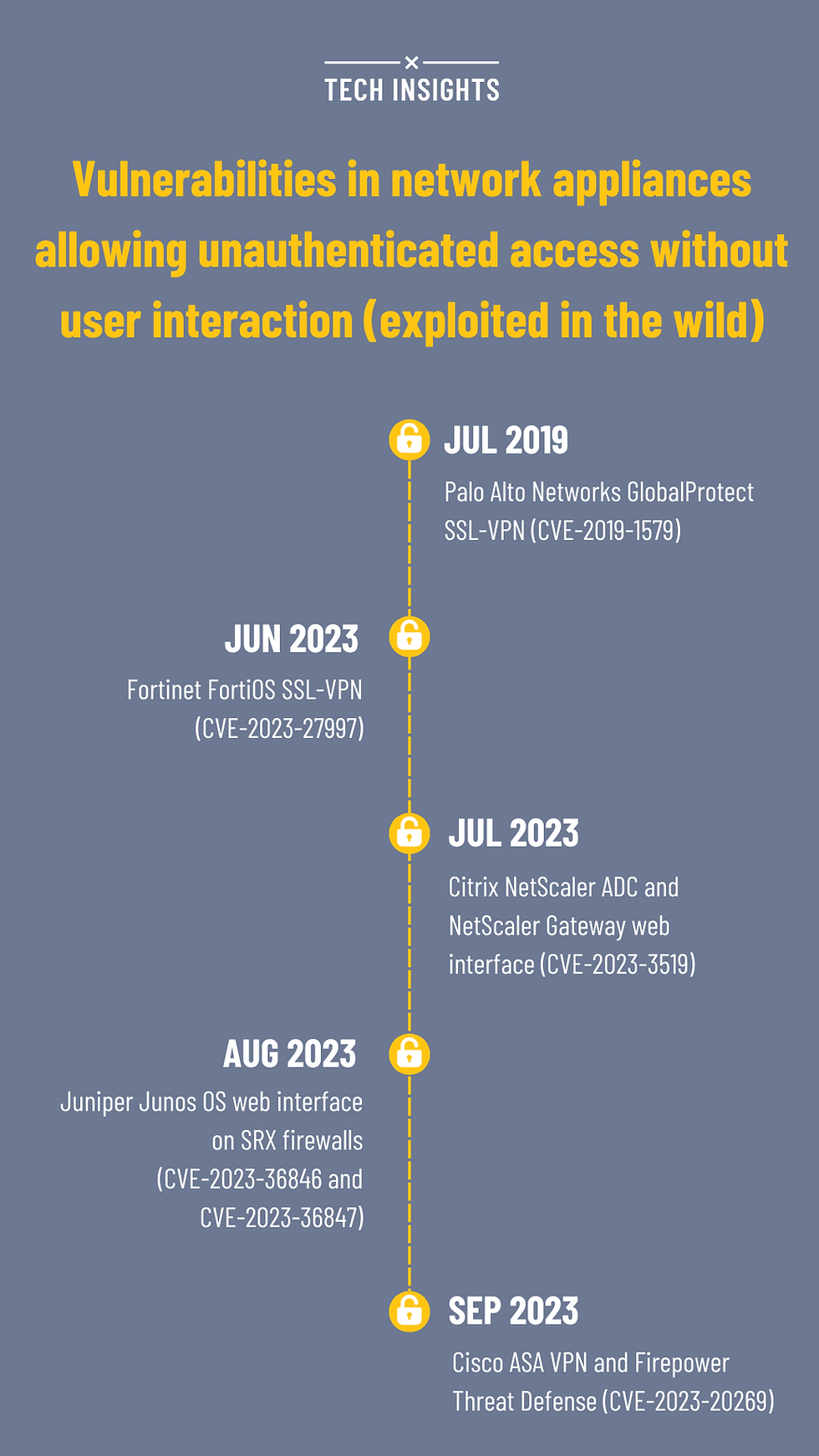
This summer has seen a flurry of vulnerabilities in network devices, from Fortinet, over Citrix and Juniper to Cisco VPN (Palo Alto's SSL-VPN bug from 2019 is now a distant memory).
These internet facing devices are being exploited more then ever before, with virtually no time between disclosure and exploitation in the wild. The exposed services such as web interfaces or SSL-VPN allow quick exploitation without user interaction, followed by device takeover and lateral movement, finally leading to ransomware and other compromises.
Evidently, the devices are a critical part of an organization attack surface. And yet, the rate of patching is still slow, suggesting inadequate maintenance and investment into managed services.
For example, the recent Fortinet bug (CVE-2023-27997) has seen devices mostly left unpatched a month after the vendor published the fix. Even today, the situation in the Adriatics region is not much better.
How many Cisco, Palo Alto, Juniper or Fortinet devices are still sitting ducks in the region, unpatched and vulnerable to attacks?
![[Webinar] NIS2 is Here - What Now?](https://static.wixstatic.com/media/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.png/v1/fill/w_250,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.webp)
![[Webinar] NIS2 is Here - What Now?](https://static.wixstatic.com/media/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.png/v1/fill/w_305,h_305,fp_0.50_0.50,q_95,enc_avif,quality_auto/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.webp)



