Supply chain risks: the MOVEit fallout is getting bigger
- Oct 5, 2023
- 3 min read

MOVEit, a file transfer management software provided by U.S. based company Progress Software (formerly Ipswitch), initially made headlines in late May 2023: a critical vulnerability (CVE-2023-34362) allowed attackers unauthenticated access and sensitive data exfiltration from thousands of servers deployed across organizations worldwide (mostly located in the USA and West Europe).
The issue with MOVEit is that it is being used by companies to allow multiple trading partners to send documents via web uploads - the goal being secure collaboration and automated file transfers of sensitive data.
For ex. a health insurance company might setup a file sharing service based on MOVEit, which allows many hospitals to upload patient documentation for insurance claim purposes. With time, a huge amount of sensitive files build up on an individual MOVEit server, affecting thousands or millions of customer records originating from multiple unrelated organizations. If data is stolen from such a server, most documents will be from organizations not directly running MOVEit software, yet still impacted.
Another key issue is that applications such as MOVEit, which provide a B2C or B2B service, are by definition publicly exposed on the internet, usually via port 443. This is similar to SSL-VPN services in firewall devices: a vulnerability in such services can suddenly make an organization wide open to attacks.
Unfortunately, many organizations are not in position to implement patches that fast. In case of MOVEit, by the time the patch was distributed and implemented with customers, it was already too late. Early June, Mandiant and other security vendors were seeing "multiple cases where large volumes of files have been stolen from victims' MOVEit transfer systems" (see here).
The attack trends speak to themselves: as an example, here's Palo Alto attack trend based on its detections at customer sites (source here):

Important to note here: customers installing and running MOVEit on-premise were hit much harder: apparently, the largest leaks originated with organizations managing their own servers, making them exposed for a much longer time.
Also, the post-breach threat hunting and cleanup effort certainly proved to be much costlier for those customers.
The SaaS version managed by the vendor (MOVEit Cloud file transfer-as-a-service) was apparenlty patched very early, probably even before vulnerability disclosure or official patch release. According to Progress Software and public records, "no evidence of unauthorized data exfiltration of cloud customers were found", although the vendor "identified the staged exploit on three of our clusters and removed it".
The customer impact
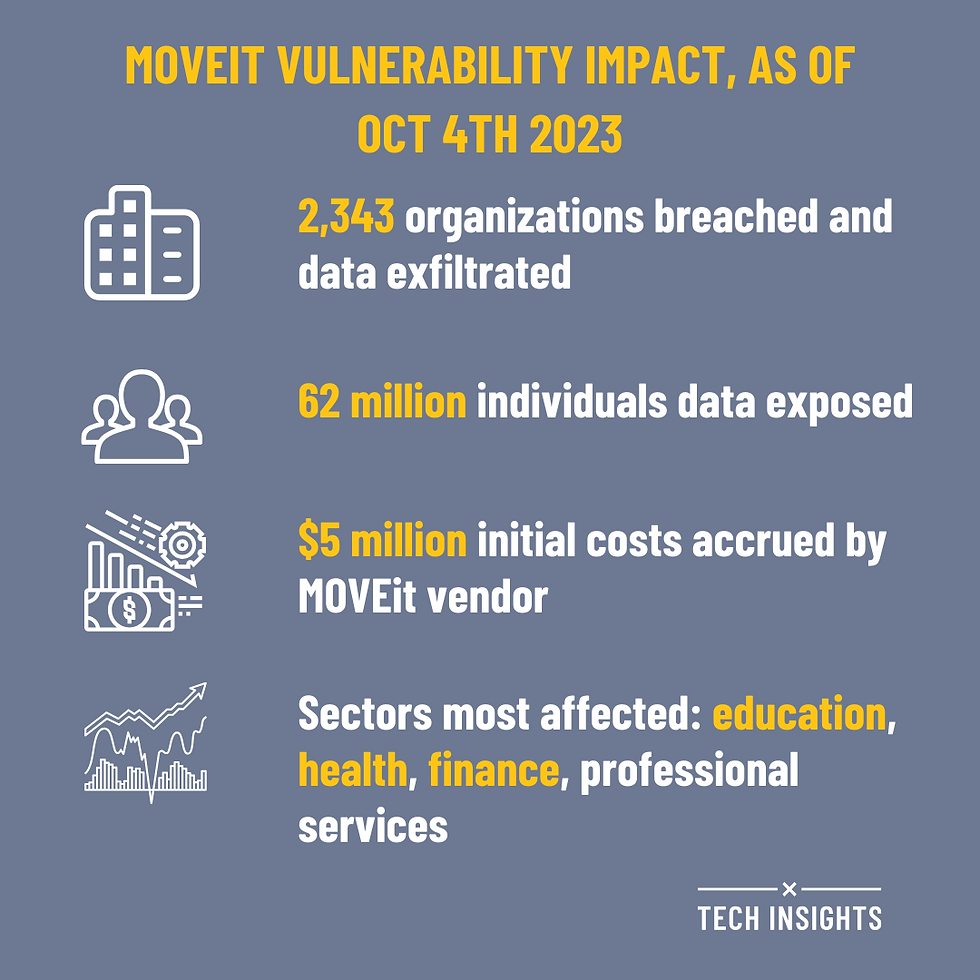
For self-managed on-prem customers relying on manual patching, the ordeal proved much costlier. Here's the damage as of early October 2023 according to Emisoft's analysis, and based on state breach notifications, SEC filings, other public disclosures, as well as the ransomware gang responsible for most of the attacks (Cl0p):
2,343 organizations breached and data exfiltrated
62 million individuals had their data exposed
most heavily affected sectors: education, health, finance and professional services
This count is bound to grow, as many organization have yet to identify the full scale of data leakage.
The impact on the vendor - Progress Software
Cyber incident and vulnerability response expenses visible in SEC filings give an indication of costs accrued so far, but also the shape of things to come:
951,000 USD in latest business quarter (ending on Aug 31st)
1,483,000 USD in previous quarter
5,126,000 USD year to date
So far, the direct impact for Progress Software is around 10% of its annual net profits. However, that does not include the mounting legal costs which will certainly hit the company once customers start demanding damages, based on customer records leaked.
These could propagate for years into the future and could be an order of magnitude higher.
When all is taken into account, it's possible Progress Software will take a hit amounting to a whole year of net income, possibly much more - a material impact indeed.
The hack, now considered the biggest of 2023, is reminding everybody of the risks and the far reaching impact when a vulnerability propagates through a supply chain. It is also a lesson for many organizations on the risks of improperly managing internet facing services, especially when a local version is run on-premise.
![[Webinar] NIS2 is Here - What Now?](https://static.wixstatic.com/media/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.png/v1/fill/w_250,h_250,fp_0.50_0.50,q_35,blur_30,enc_avif,quality_auto/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.webp)
![[Webinar] NIS2 is Here - What Now?](https://static.wixstatic.com/media/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.png/v1/fill/w_305,h_305,fp_0.50_0.50,q_95,enc_avif,quality_auto/6681e7_beb47411e54f424c8b934c85bd5b487b~mv2.webp)



